I joined Lemmy back in 2020 and have been using it as [email protected] until somewhere in 2023 when I switched to lemmy.world. I’m interested in systemd/Linux, FOSS, and Selfhosting.
- 75 Posts
- 76 Comments
It was, it was really disapointing

 3·1 day ago
3·1 day agoHave you considered that the machine is made by a collection of humans?
The metadata showed it was edited in Adobe Premiere and was a combination of several other videos. As AstralPath said, Coffeezilla (a YouTuber primarily known for exposing and investigating crypto scams) has a video about it on his second channel.

 0·3 days ago
0·3 days agoYes, as it doesn’t even boot up an OS in the background.
Do you mean the desktop environment?
Some person was showing me videos of him and telling me he was very smart, does anyone happen to know some good examples to get him to reconsider?

 4·4 days ago
4·4 days agoThanks, I didn’t know about that

 2·4 days ago
2·4 days agoYes, but I still don’t know why they seem to think it’s so important to write a new browser engine instead of improving Gecko or Servo. To me it just seems like people like it because they don’t know other things aside from the Chrome, Safari, and Firefox browser engines exist and just chase something new and shiny.

 0·4 days ago
0·4 days agoThis is a great initiative! I tried plasma on a tablet like device a while ago and the keyboard was one of the main issues holding it back.

 5·4 days ago
5·4 days agoAnd obviously their option is the “best”. From the conclusion:
Talos Linux is unique. It’s the only option that includes OS management in a purpose-built distribution for running Kubernetes. There’s no compromise for scaling up or down. In terms of small-scale numbers, it “wins” in several of the examined categories, including memory usage, disk r/w, and installation size. But all of these metrics are side effects of Talos Linux’s defining characteristic: It’s simple.

 0·4 days ago
0·4 days agoThe find out phase took it’s time

 6·4 days ago
6·4 days agoThe fact that it’s aiming to be stable doesn’t mean it is. It’s still a work in progress unlike other browsers.
What a wholesome interaction 😃
No that doesn’t seem to be it. Thanks for trying anyway.
When the program is running it’s probably stored with 32 or 64 bits, but that probably isn’t the case for the network packet layout. I can imagine them wanting to optimize network traffic with over 3 billion users even if it’s just a small improvement.
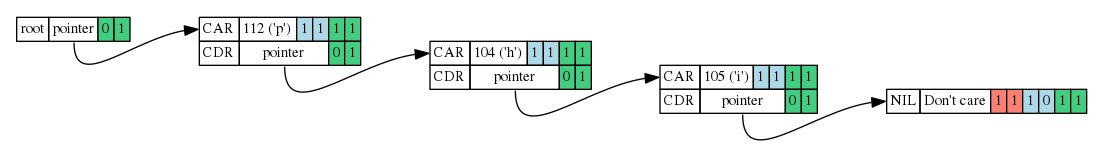
Also TIL that Erlang’s VM apparently stores strings as linked lists of chars. Very strange.
As the numbers guy. Do you remember the name of the site that can tell you the what a given number is often associated with?
At some point they l announce that paying for a Reddit premium account allows you to be unbanned and free to do whatever you want.
What other reasons or ideas can you think of, that mass banning users, (some with years of age and contributions, some of them mods.) could be the first step in a plan to capitalize.
To me it seems like it’s a consequence of both cost cutting moderators and lowering the threshold for bans to make the plaform more appealing to large companies advertising.

 201·7 days ago
201·7 days agoFYI you can get a numeric xyz domain for 1$ a year
…definitely takes some getting used to when you come from a non-memory safe language…
I actually think it’s more like the opposite. The compiler takes the normal rules you apply to avoid issues with a non-memory safe language like C/C++ and enforces them explicitly where memory safe languages don’t have those rules at all. I think lifetimes are much more confusing if you’ve never dealt with a user after free and usually let GC deal with it.
Also yes the compiler warnings and errors are amazing, the difference between rustc and gcc is night and day.

 2·7 days ago
2·7 days agoI don’t really prefer it. I just buy gaming mice because they have more buttons and disable the RGB.




















It is