Just a fun, somewhat terrifying read
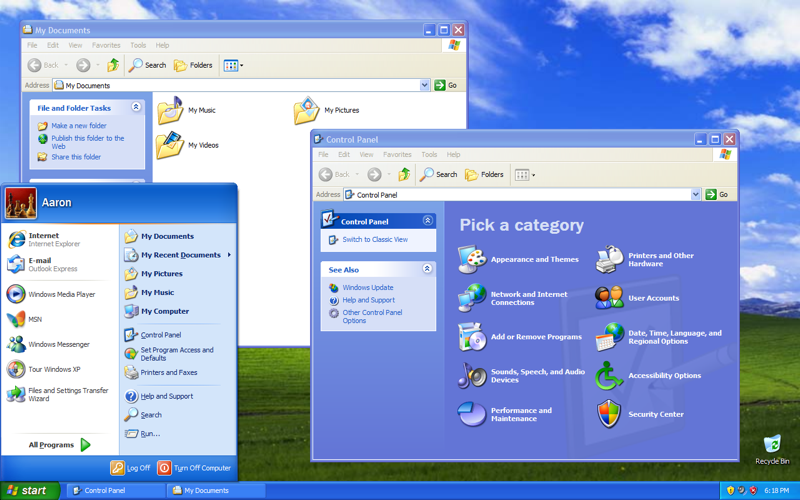
Wow, Windows is better! Look at how fast you can set up an FTP server, without even issuing any commands!
Beat that, Linux!
This is a top tier joke
Torvolds adding neuralink kernel support /s
About 15 years ago I left a PC running an ftp server with no password. Weeks later I went to use it and it had 0 disk space. The drive was filled with PS2 isos.
Thanks hackers!
delet
I can write an ansible playbook to do it. Probably just pull in a container
A bit clickbaity…
configured it to be fully exposed with no firewall and no anti-virus software
And I’m also assuming this was then exposed directly to the internet like a server, not behind a NAT or anything like that.
I mean you’re setting up a 20 yo unpatched consumer lever OS to fail for the giggles and you kneecap it on top of it - which is fine, but hardly surprising.
I bet they just threw it into the DMZ, turns out when you park your car in a bad part of town and leave all the windows open and the doors unlocked, bad stuff happens to it
And the keys in it, with a light on top flashing “look at me!”
Honestly, I’d be a little surprised if anyone actually did anything to it.
Not for lack of wanting to, but because they, like me, would probably just assume it’s a bait car and cops are 5 seconds away with a kill switch.
There’s tons of botnets in countries that don’t care about cyber crime just waiting for this sort of thing to be put on the internet. They’d just autopwn as soon as it was discovered and don’t really give a shit since the cops can’t even touch them.
And I’m also assuming this was then exposed directly to the internet like a server, not behind a NAT or anything like that.
That’s how consumer PCs were often setup back in the early XP days though. There was a time when a household typically didn’t have more than one computer or internet connected device. So people didn’t have a NAT-ing router and instead connected their DSL or cable modem directly to their PC, and were completely exposed to the internet. To make matters worse, the firewall was disabled by default in early XP versions as well, until SP2.
This is how Sasser and the Blaster worm were able to wreak havoc, and until home routers started to become common, it was a genuine concern that on a new XP installation you’d be hacked before you had time to patch.
In the early days we learned a lot of things about security through trial-and-error, basically running head-on into the issues, and then going “oh…”.
This isn’t a test of the “early days” XP and internet. This is a test of current day, because clearly the implication is “look how bad it is to use XP in 2024”
Was it disabled? I thought that XP just didn’t have a firewall and got one added later on. I forget which virus it was but RPC would crash within seconds of a device being connected to the internet meaning you had to reboot.
Edit
Apparently it was MSBlaster
According to Wikipedia, it used to be called Internet Connection Firewall in early versions of XP and then was rebranded to Windows Firewall and turned on automatically in SP2.
And yet XP is still running god knows how many major company systems (air gapped of course, but still).
I would expect there to be problems with most machines if they were to be fully exposed to the internet, nobody actually uses a computer like this
My router is a computer connected to the Internet. Yours probably is too.
your router is not running windows XP with the firewall turned off
In fact, it is the firewall that separates your network from the internet, it’s the first line of defense that would normally provide some protection for an exploitable machine
I know that. Re-read the post I replied to.
Didn’t someone implement a virus at some point that propagated through sound from speakers to microphones?
That was a way to offload information from an air gapped system. It already has to be compromised to work
IIRC that was not proven and the researcher who made that claim had some mental illness? Idk
To be fair, if we discredited research from individuals with mental illness half of our research would be gone.
But yeah, it was mostly a proof of concept of someone happened to plug a bad USB into an air gapped machine with a mic and speakers
Oh yea, I was consulting in a factory recently and one production line was running off of Finnish windows XP with no service packs because the software for the machines doesn’t support anything else.
Security research is interesting. Exploits get fixed but not everyone updates their software and not every company ensures their software isn’t vulnerable to them. So there are programs that will run through every known vulnerability and test if the target is vulnerable. They’ll check for old exploits that work on Windows XP and Internet Explorer 6. Apparently it’s not uncommon to find large enterprises still running these.
The XP stands for eXPloit.
Damn just imagine this being the old net. With viruses still roaming the digital waterfront eager to infect and eat anything that is foolish enough to breach in.
This makes me think of the Blackwall in Cyberpunk 2077. That game felt too real while I was playing it and I’m not looking forward to more of it feeling real as time goes on
Doesn’t a bunch of military equipment still run WinXP?
U.S. military doesn’t run standard versions of Windows and many if not most military terminals don’t connect to World Wide Web.
Not perfect but if it’s only connectd to Army intranet, might not be vulnerable?
That question mark instills a lot of confidence.
The biggest vulnerability in most computer systems are people. Many Soldiers are too lazy to save or encrypt thier files and lose them or comprise them all the time.
A computer system that isn’t designed to and doesn’t need to connect to the World Wide Web should be safe. If no one, for example decides they want to access a certain civilian website and so finds a way to connect their terminal to the World Wide Web, compromising it.
I’m sure you’re aware, but the internet and the “world wide web” are different things. The common term for what you’re describing is air gapping.
Yes, world wide web isn’t the right term in this case. Proper term is just internet and it is an air gapped network.
ah, Military “Security”.
Neat, didn’t know that and am unfortunately not very surprised. Yeah, can, on paper, design robust SOPs and machines, then set the passcode to 0.
Embedded systems may technically run an OS or on and OS, but they’re really their own thing.
Can you expand on this with some more detail?
I’ve worked on DoD networks continuously since 2011 and nothing you said is true, provided I understood you correctly.
I am more referring to the U.S. Army intranet system. Which while some services can be accessed from the internet, some can only be accessed while connected to the Army Intranet. The Amry uses alot of terminals, computers, that have no need to connect to the internet but only the Army intranet.
Also, the Army modfies some of the programs and hardwere they use, such as Windows from their standard commercial versions, removing or changing features and such.
Well that guy’s network and all of his friends too are now compromised. Good job.
I guess you missed the bit about it running on a virtual machine, huh?
I guess you have no idea about Virtual Machine escape, huh?
Actuall, no. If a VM can be broken, how come everyone goes on about things being perfectly safe to run in one?
It gives people like me a false sense of security.
Exactly. And you can see by the number of upvotes your comment got vs the number of downvotes earned by mine that a false sense of security is shared by the majority.
Well I for one, stand corrected.
VM does not mean it is safe. There is malware out there that can break the sandbox and infect the hypervisor
Such an exploit would not get wasted on some random xp honeypot
It’s XP, there are likely several unpatched escaping bugs with free POC out there. You don’t need anything new.
Surely breaking out of a VM requires exploiting a vulnerability of the VM, not of the OS running in it?
I would assume it requires both a hypervisor and guest OS bug to be tripped.
It’s pure speculation, but I assume you’ll need
- Enough access to the guest OS so that you can interact directly with the virtual hardware. That would probably require root access, so you’ll probably need to exploit some bug in the guest OS to get there.
- To break out of the vm, you’ll then need to exploit a bug in the virtual hardware. You would want to get the hypervisor to execute arbitrary code.
- If you want to infect the host OS, then you’ll need sufficient access on the host. If the hypervisor doesn’t run with sufficient privileges, you’ll have to exploit a bug in the host as well to perform a privilege escalation. But I’m guessing the hypervisor will usually have sufficient privileges, so exploiting the host is probably not necessary.
Sounds like quite a bit of work, but I don’t see why malware couldn’t automate it. An up-to-date hypervisor should help reduce the risk though.
It’s XP. There’s guaranteed to be a way to go from userland to ring 0 code execution.